
Polygon is a layer 2 scaling platform built on top of the Ethereum network with added layers and independent blockchain harnessing Ethereum's security. Polygon uses EVM compatibility and leverages its security to migrate and liberate Ethereum projects to the Polygon network.
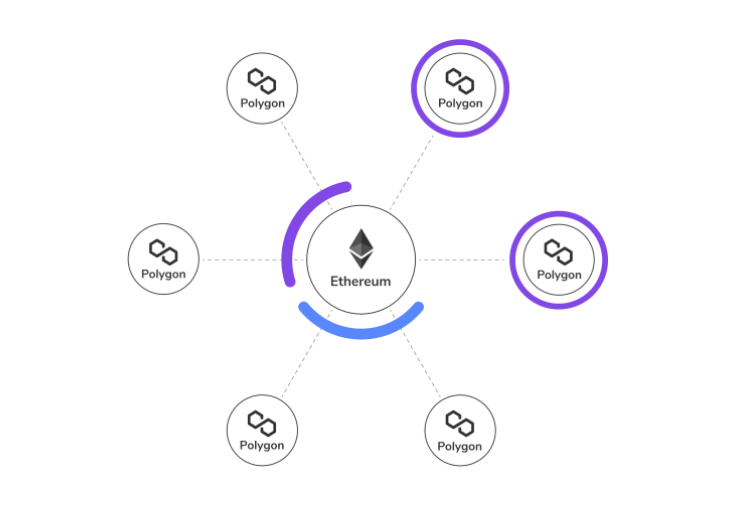
Polygon is a multi-chain blockchain solution that runs parallel to Ethereum that can help projects to achieve autonomy, create their own chains, and scale their projects on multiple chains while using Ethereum security, interoperability, and developer resources.
Yes, Polygon is still a side chain but much more capable and independent, which has scaled to an Entire ecosystem whilst being a side-chain to Ethereum. The transaction fee is lower, the speed is more, and scalability options are much more than Ethereum provides.
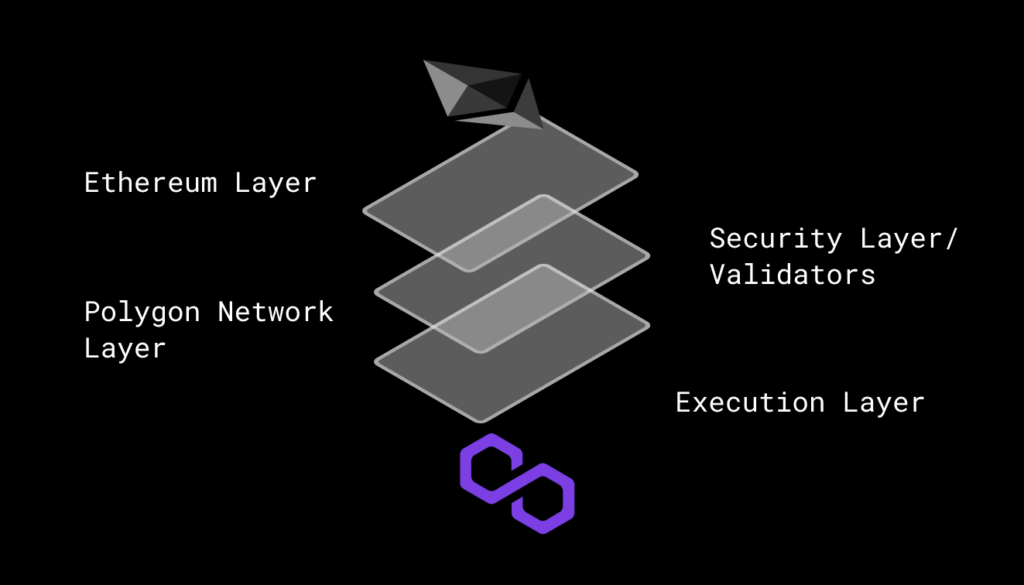
Polygon allows Ethereum based blockchains freedom to scale and shift into independent chains and multi-chain solutions whilst remaining secure using Ethereum network security. It is safe to assume that Polygon is a protocol and a gateway to solve scalability and provide multi-chain solutions to Ethereum applications.
Polygon makes blockchains EVM (Ethereum virtual machine) capable but independent from Ethereum, removing Ethereum and running Polygon as the base coin for transaction fee. Polygon is currently running a native bridge in order to migrate Ethereum tokes to the polygon network.
Polygon has Proof of stake, zk Rollup, optimistic rollup chains, and more in development. There is also a dev net called avail for standalone chains, side-chain, and off-chain scaling solutions. Enterprise chains are in development for institutions to scale ERP solutions and databases.
Polygon is also a developer-friendly platform just like Ethereum. The core idea is to equip developers with tools to scale single-chain projects into multi-chain projects. The code resources are open source and developers are encouraged to develop dApps and networks on Polygon.
There are grants and other options to help developers bring forward new solutions to the network. Regular bug bounty campaigns are held to identify any problems in the security of the network, specific to security issues.
